Have a suggestion?
Click here to suggest a blog item.
Newsletters Archive
Catch up with DonationCoder by browsing our past newsletters, which collect the most interesting discussions on our site: here.
Editorial Integrity
DonationCoder does not accept paid promotions. We have a strict policy of not accepting gifts of any kind in exchange for placing content in our blogs or newsletters, or on our forum. The content and recommendations you see on our site reflect our genuine personal interests and nothing more.
Latest News
July 2, 2024
Server Migrations Coming
- Donationcoder server migration is slowly proceeding, expect some hiccups as we get all our ducks in a row..
July 19, 2022
Software Update
Jan 3, 2022
Event Results
May 13, 2020
Software Updates
Mar 24, 2020
Mini Newsletter
Dec 30, 2019
Software Updates
Jan 22, 2020
Software Updates
Jan 12, 2020
Newsletter
Jan 3, 2020
Event Results
Jan 2, 2020
Software Updates
Dec 30, 2019
Software Updates
- Automatic Screenshotter v1.16
- Screenshot Captor v4.35 beta
- Find and Run Robot v2.238 beta
- Clipboard Help and Spell v2.46.01
- LaunchBar Commander v1.157
- Mousers Media Browser v2.0
- MultiPhoto Quotes v2.09.1
- DiscussionList for Android v1.08
April 27, 2019
Software Updates
Feb 26, 2019
Software Updates
Feb 23, 2019
Software Updates
Feb 14, 2019
Software Updates
Jan 6, 2019
Event Results
Dec 2, 2018
Software Updates
Nov 13, 2018
Software Releases
July 30, 2018
Software Updates
June 24, 2018
Software Updates
June 6, 2018
Software Updates
Apr 2, 2018
Fundraiser Celebration
Apr 2, 2018
Software Updates
Feb 24, 2018
Software Updates
Jan 14, 2018
Major Site News
Jan 10, 2018
Event Results
Latest Forum Posts
May we recommend..
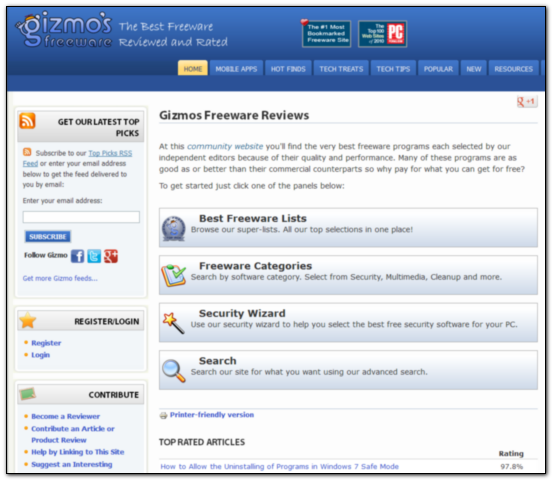
No site does as good a job of helping you choose a freeware tool for a specific task than Gizmo's Freeware (otherwise known by us old-timers as Tech Support Alert).
The site is simply unrivaled in terms of recommendations for freeware, and if you ever find yourself asking what the best free windows utility is for a given task, it's *the* site to visit.
In each well-organized category, top alternatives are reviewed, rated, and ranked, and then discussed by all -- and reviews are frequently revisited and updated, which is a rarity.
In addition, Gizmo Richards himself has also long been a friend to freeware authors, helping to shine the light on new freeware tools, and a friend to us from the early days, helping to tell people about DonationCoder and our software -- and I am extremely honored to have had some of my tools recommended on the site.
I can't think of a better site to receive the first entry in our list of our Favorite Websites.
Our daily Blog
This page spotlights the most interesting posts collected from our forum every day.
NANY 2023 Section is upNew Apps for the New Year 2023
Where everyone is invited to create new free software to share. |
||
New Technomoan youtube video on 2-xlA very well known youtuber just made a nice video on the 2-xl toy: https://www.youtube..../watch?v=amuRIydCoJk |
||
Book on kickstarer: 50 Years of Text GamesOn kickstarter now: 50 Years of Text Games: From Oregon Trail to A.I. Dungeon https://www.kickstar...-years-of-text-games |
||
MiniReview: Inspire WriterWhy have I never heard of Inspire Writer?
(I suppose another way of thinking about it, is 'how did I hear about it now?' and I'm not sure I can answer that either. It's a minimalist wysiwygish markdown editor. And I really mean minimalist. Minimalist in looks, minimalist in features and virtually no settings that can be tweaked. Though not minimalist in cost - it's not expensive but it is paid software whereas most markdown editors on Windows are free. $30 atm, same price as iA Writer. Many similarities to iA Writer and Ulysses to my untutored eye as a non-Mac user who tried the iA Writer trial, but never felt any value in using it. It feels as if there's a macness about it. I like the dark theme (which is what I use) much better than the iA Writer theme which always felt to starkly black and contrasty. This one is remarkably similar in tone to my preferred theme on Obsidian (Obsidian Nord).
Looking at the above, it looks much more limited than all the free editors I, and most people, use. So why would anyone consider paying money for it? Well, it actually looks like a neat little editor for writers. It has the necessary features (bar underline and folding) but isn't weighed down by the tonnes of useless garbage most markdown editors smother themselves with. It looks nice and easy on the eye (though would benefit from a focus mode - FocusWriter would be a good implementation; maybe adding a sentence option). There are four predefined tags - Urgent, ToDo, Draft and Published - which points to writers being their target market. And it does have useful features. There's an option for live spellchecking in up to three languages (not that this is something I often turn on). There are statistics for selection and whole document (characters, sentences, paragraphs, pages - though I'm not sure how the pages are calculated). There's a comment syntax (++ for a line/section; %% for blocks) There's a very nice set of export options - Ghost, Medium, WordPress (+ PDF & HTML) and especially .docx. I really like this one. It presents the option of exporting into a number of styles (Modern, Elegant, Formal etc), allows a preview, and then the options are to save, to put into clipboard or to open in a selected program - such as Word. So no need to create documents if that's not needed, which suits my Workflowy purposes ideally - though I still need to do my copying from Word itself to get the paragraphs I need - Enter appears to = New Paragraph; with Shift-Enter = New Line, but the 'paragraphs' are really markdown lines, and the new lines are soft line breaks. Autosave is quite fast (at least in external files) and it has a regular backup schedule. So all that's quite nice. And all of that is for files living in the file explorer, being shared with other editors. There are a few more features, for those files created in or imported to the Library. (I assume that the library is some type of database. Imported files stay where they are, there's just a new copy created in the library; the new copy is not synchronised with the original file.) Possibly the most important of these is that the files in a Library folder can be moved around the sequence easily and that individual files can be selected for export using the usual Ctrl or Shift options, which makes it very easy to put together a long document/book for export to Word or PDF. These 'sheets' can also be split or merged as desired. There's also a note/sticky note feature (only one per sheet) and session word counts (and goals). Do I like it? Yes I do. Despite the lack of folding, I can imagine using it as my main writing interface. The export options to Word are great. It's very simple; all the options it has are useful to me (most writers, I imagine) and there's nothing else getting in the way. For those that want them, the Scrivener like scene/chapter/book type options seem functional. It happily works as a normal markdown editor on external files as well as those in its database, though with slightly fewer features (I think its file explorer gives it an advantage over WriteMonkey 3 in this regard). I'm happy to buy it for my writing and happy to use the other editors for notes and anything that needs their more advanced capabilities. I came across the following review, which specifically compares it to Ulysses, so I feel that my impression of macness is probably on the mark. |
||
Opinions requested on my new YouTube Video SeriesI've recorded a 5+ hour (16 part?) video series called "Micro-studio Boardgame Video Production": https://www.youtube....dS3u1bo7zW80rt-d3bDr First episode: It covers most of what I've learned in the last year. It's not live yet, I still have another 10 days or so before I make it live, and I'd love any feedback about things that I should fix before making it live! Let me know your suggestions. |
||
Deskreen - nice free tool for sending (teleprompter flip) pc window to a tabletWent looking for a straightforward tool to let me broadcast one of my pc screens to an android tablet during a recording -- with the additional need to be able to flip/mirror the screen in the process for a teleprompter effect. Came across Deskreen which seems to work well and is free (donations encouraged): https://deskreen.com/ |
||